ai-ta
Autonomous Infrastructure Triage Agent
AI investigates. Humans decide. Infrastructure learns.
The problem
Platform ops runs 8-5. Infrastructure runs 24/7.
The 15-hour gap means overnight incidents go undetected until morning — often after they've cascaded into application outages that wake up the wrong team. NIS2 Article 20 makes the board personally liable for incident response capability you don't have outside business hours.
How it works
Alert → Investigate → Resolve → Learn → Repeat
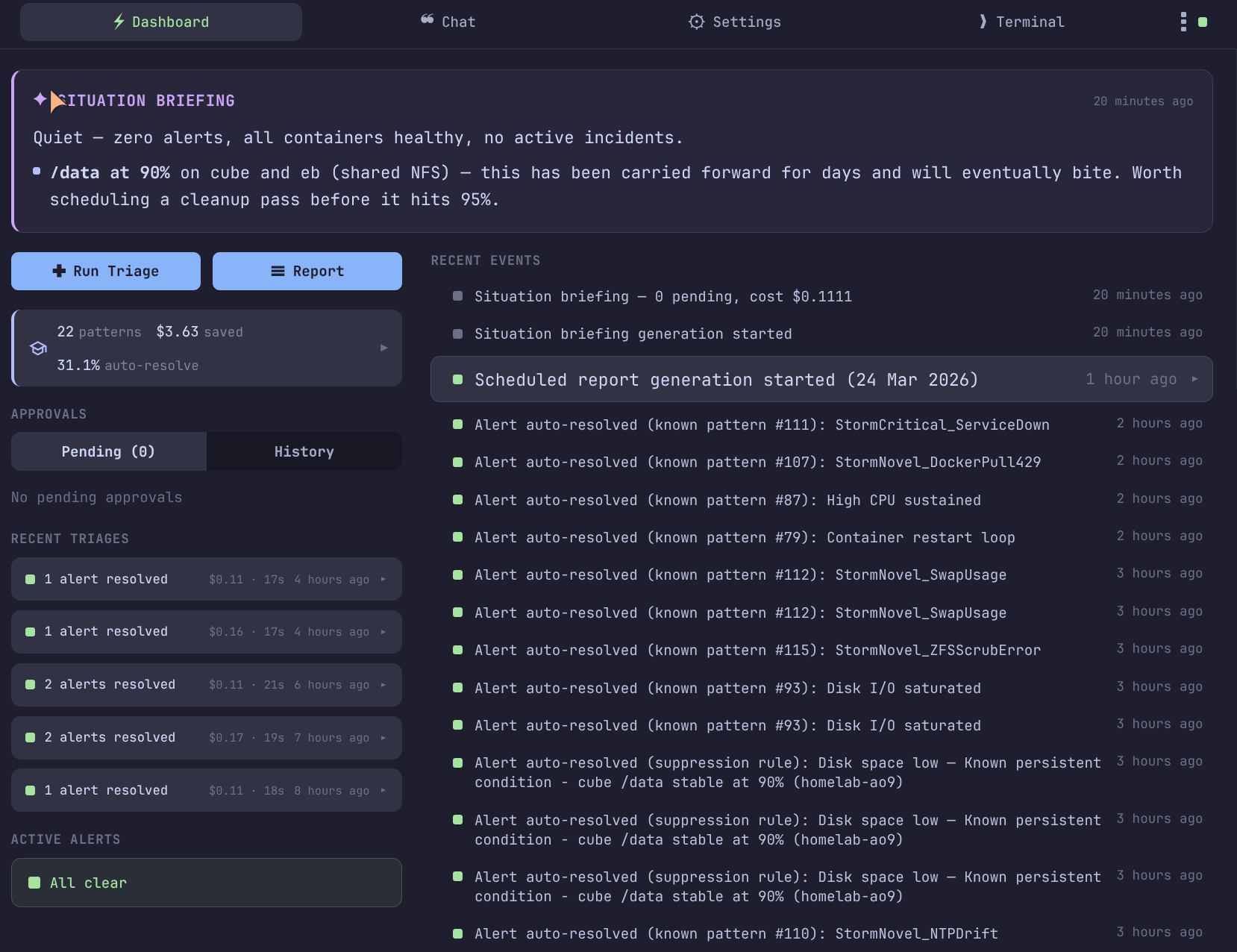
By the numbers
Real data from production
Compliance
NIS2 & GDPR ready
Integration
Works with what you have
Where operations is going
Software stops being the constraint
The operator's job becomes steering processes, owning accountability, and managing risk — not navigating dashboards. Three shifts are converging:
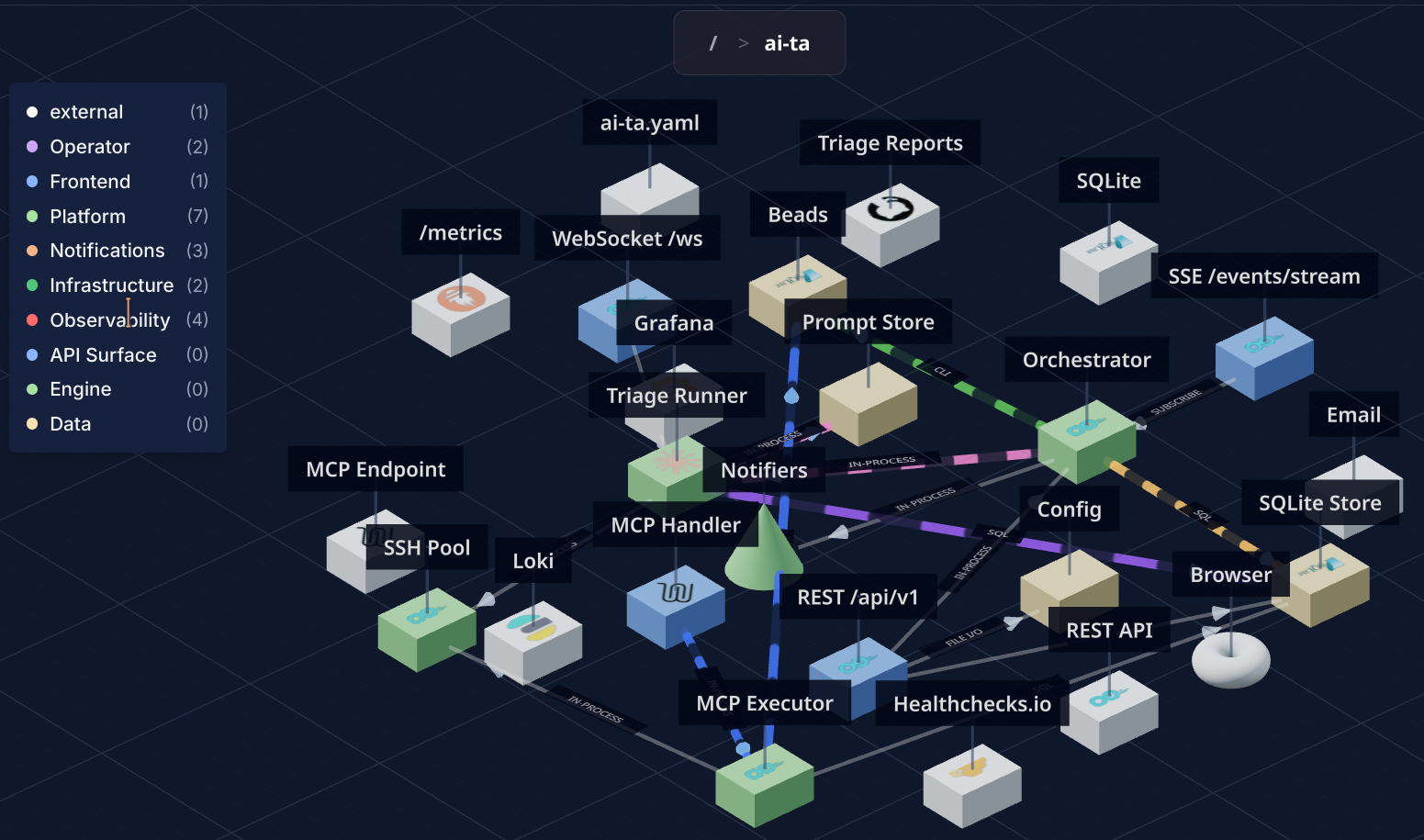
Machine-to-machine by default
Monitoring talks to triage, triage talks to remediation, remediation talks to approval gates. Humans intervene at decision points, not execution points. Contracts and schemas enforce determinism between autonomous systems.
Frontends become contextual projections
What matters isn't how the UI looks — it's that the right information reaches the right person at the right moment. A morning email, a mobile approval, an MCP query from another agent — all valid interfaces.
Governance becomes the product
When AI acts autonomously, the value is the audit trail, the approval gates, the policy enforcement, the explainability. The strictest compliance environments aren't obstacles — they're the reason it must be built this way.
ai-ta is built for this future
Governance-first autonomous operations
Scope & boundaries
ai-ta contains incidents. It never makes irreversible decisions.
Observes across every layer. Contains with human approval. The boundary is reversibility and blast radius.
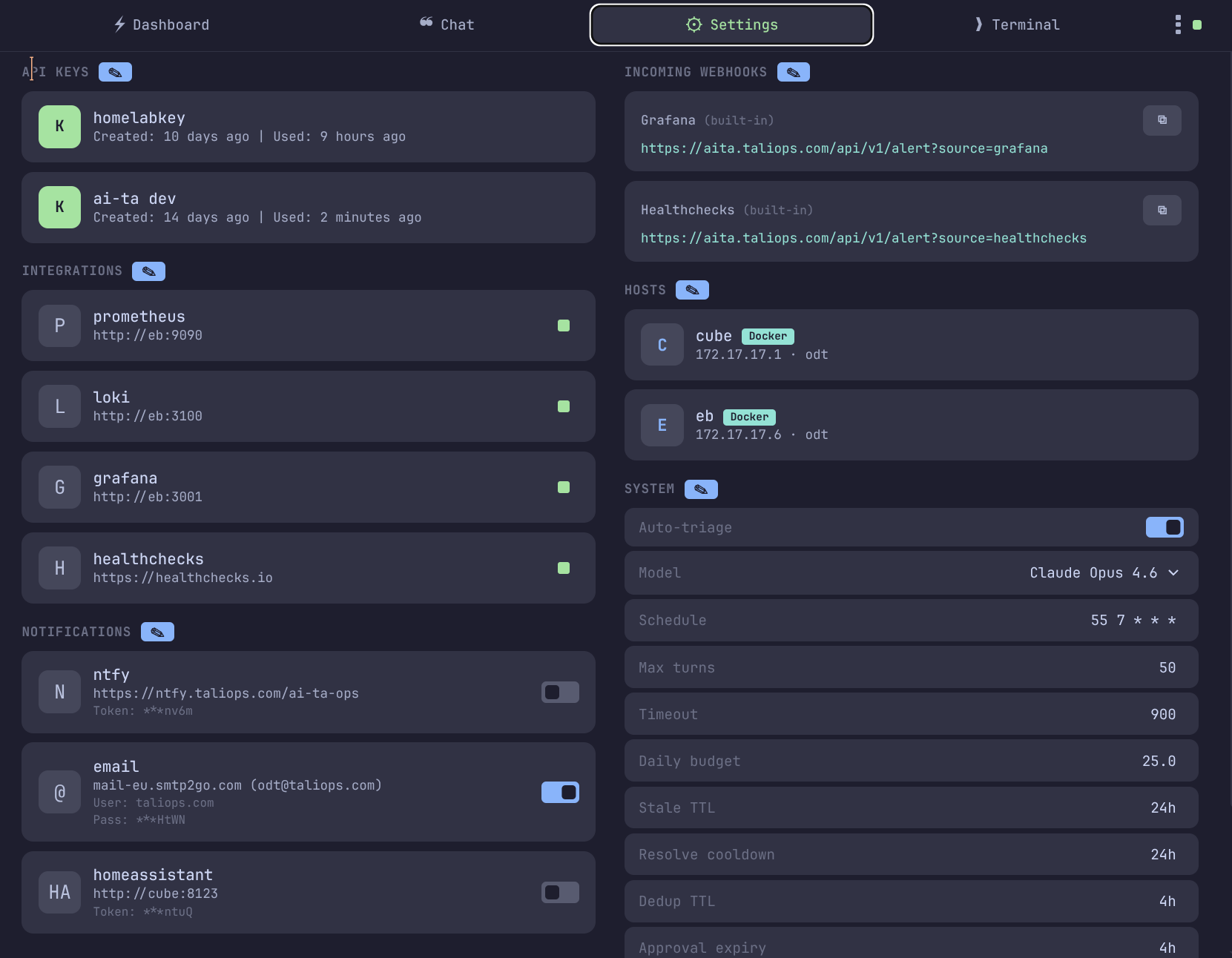
Single container
- One Go binary, one YAML config, one SQLite database
- Deploys in minutes — Docker, Kubernetes, or OpenShift
- Your data stays in your network
- AI governance from a git repo your CISO controls
- Helm chart ready for enterprise orchestrators
Get started
Deploy in minutes. No sales call.
ai-ta is source-available and free to evaluate. Pull the image, point it at your infrastructure, get your first triage report. Subscribe when you're ready for production support.
Evaluate
docker compose up. Connect Grafana. First triage report in 15 minutes. Full product, no feature gates.
Subscribe
Priority updates, security patches, guaranteed LLM compatibility. Per-host or flat-rate pricing.
Enterprise
Dedicated onboarding, governance co-development, NIS2 compliance review, DPA.
AITA for letting an AI handle my on-call?
NTA. Your infra, your rules.
Live demo on running infrastructure. Not slides — the real system investigating real alerts.
Download pitch deck (PDF)Let's talk
Ready to see autonomous infrastructure triage on your infrastructure?